|

|
|
ActiveSocket Network Communication Toolkit by ActiveXperts Software - HTTP, HTTPs, FTP, ICMP, SNMP Get/GetNext/Set, SNMP Traps, NTP, RSH, Telnet and more
|
 Visit ActiveSocket Web Site Visit ActiveSocket Web Site
 Download ActiveSocket Network Communication Toolkit Download ActiveSocket Network Communication Toolkit
Network Basics: LAN, WAN, VPN
A network is a system of hardware and software, put together for the purpose of communication and
resource sharing. A network includes transmission hardware, devices to interconnect transmission media
and to control transmissions, and software to decode and format data, as well as to detect and correct problems.
There are several types of networks in use today. This chapter will focus on three of them:
- LAN - Local Area Network
- WAN - Wide Area Network
- VPN - Virtual Private Network
LAN
The most widely deployed type of network, LANs were designed as an alternative to the more expensive
point-to-point connection. A LAN has high throughput for relatively low cost. LANs often rely on shared
media, usually a cable, for connecting many computers. This reduces cost. The computers take turns
using the cable to send data.
Repeaters and Bridges
LANs typically connect computers located in close physical proximity, i.e., all the computers in a building.
Repeaters are used to join network segments when the distance spanned causes electrical signals to
weaken. Repeaters are basically amplifiers that work at the bit level; they do not actively modify data that
is amplified and sent to the next segment.
Like repeaters, bridges are used to connect two LANs together. Unlike repeaters, bridges work at the
frame level. This is useful, allowing bridges to detect and discard corrupted frames. They can also perform
frame filtering, only forwarding a frame when necessary. Both of these capabilities decrease network congestion.
Bridged LANs can span arbitrary distances when using a satellite channel for the bridge. The resulting network
is still considered a LAN and not a WAN.
WAN
To be considered a WAN, a network must be able to connect an arbitrary number of sites across an arbitrary
distance, with an arbitrary number of computers at each site. In addition, it must have reasonable performance
(no long delays) and allow all of the computers connected to it to communicate simultaneously.
This is accomplished with packet switches.
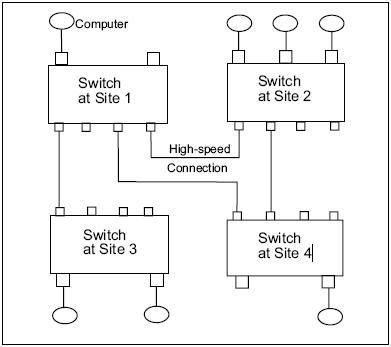
Picture 1: WAN with 4 Switches.
Packet Switches
Packet switches are small computers with CPUs, memory and I/O devices. They move complete packets,
using a technique called Store and Forward. An incoming packet is stored in a memory buffer and the CPU
is interrupted. The processor examines the packet and forwards it to the appropriate place. This strategy
allows the switch to accept multiple packets simultaneously.
As the figure above illustrates, WANs currently do not need to be symmetric.
Forwarding a Packet
A data structure contains the information that tells the switch where to send the packet next. This is called
a routing table. The destination address in the packet header determines the routing table entry that is used
to forward the packet. It could be forwarded to a computer attached to the switch that is examining the
packet or it could be to another switch in the WAN.
VPN
VPNs are built on top of a publicly-accessible infrastructure, such as the Internet or the public telephone
network. They use some form of encryption and have strong user authentication. Essentially a VPN is a
form of WAN; the difference is their ability to use public networks rather than private leased lines. A VPN
supports the same intranet services as a traditional WAN, but also supports remote access service. This is
good for telecommuting, as leased lines dont usually extend to private homes and travel destinations.
A remote VPN user can connect via an Internet Service Provider (ISP) in the usual way. This eliminates
long-distance charges. The user can then initiate a tunnel request to the destination server. The server
authenticates the user and creates the other end of the tunnel. VPN software encrypts the data, packages it
in an IP packet (for compatibility with the Internet) and sends it through the tunnel, where it is decrypted at
the other end.
There are several tunneling protocols available: IP security (IPsec), Point-to-Point Tunneling Protocol
(PPTP) and Layer 2 Tunneling Protocol (L2TP).
Network Devices
Some network devices (repeaters, bridges and switches) were discussed in the previous sections. These are
all dedicated hardware devices. Network devices can also be non-dedicated systems running network software.
Routers
A router is a hardware device that connects two or more networks. Routers are the primary backbone
device of the Internet, connecting different network technologies into a seamless whole. Each router is
assigned two or more IP addresses because each IP address contains a prefix that specifies a physical network.
Before a packet is passed to the routing software, it is examined. If it is corrupted, it is discarded. If it is
not corrupted, a routing table is consulted to determine where to send it next. By default, routers do not
propagate broadcast packets. A router can be configured
to pass certain types of broadcasts.
Firewalls
A firewall is a computer, router, or some other communications device that controls data flow between networks.
Generally, a firewall is a first-line defense against attacks from the outside world. A firewall can be
hardware-based or software-based. A hardware-based firewall is a special router with additional filter and
management capabilities. A software-based firewall runs on top of the operating system and turns a PC
into a firewall.
Conceptually, firewalls can be categorized as Network layer (aka Data Link layer) or Application layer.
Network layer firewalls tend to be very fast. They control traffic based on the source and destination
addresses and port numbers, using this information to decide whether to pass the data on or discard it.
Application layer firewalls do not allow traffic to flow directly between networks. They are typically hosts
running proxy servers. Proxy servers can implement protocol specific security because they understand the
application protocol being used. For instance, an application layer firewall can be configured to allow only
e-mail into and out of the local network it protects.
Gateways
A gateway performs routing functions. The term default gateway is used to identify the router that connects
a LAN to an internet. A gateway can do more than a router; it also performs protocol conversions
from one network to another.
Network Architecture
There are two network architectures widely used today: peer-to-peer and client/server. In peer-to-peer networks
each workstation has the same capabilities and responsibilities. These networks are usually less
expensive and simpler to design than client/server networks, but they do not offer the same performance
with heavy traffic.
Client/Server Networks
The client/server paradigm requires some computers to be dedicated to serving other computers.
Port numbers are the mechanism for identifying particular client and server applications. Servers select a
port to wait for a connection. Most services have well-known port numbers. For example, HTTP uses port
80. When a web browser (the client) requests a web page it specifies port 80 when contacting the server.
Clients usually have ephemeral port numbers since they exist only as long as the session lasts.
|
|